You Know Phishing, But Have You Heard of Vishing & Smishing?
Originally published October 5, 2020
October is Cybersecurity Awareness Month and this month we’re bringing attention to the rise of scams, phishing attacks and social engineering. Your data’s health matters, stay cyber-healthy and take care of your data.
You may be familiar with phishing, but have you heard of smishing and vishing? Cyber criminals are always seeking out new opportunities to gain access to your personal data and these are other variants of phishing you may have encountered. Outsmart cyber criminals, stay aware and stay vigilant. The more you know, the more you can stay safe.
What is phishing?
Phishing is when a fraudulent email is sent from a seemingly legitimate organization in an attempt to convince individuals to divulge personal information, such as passwords and credit card numbers. Links in phishing emails will often take you to phoney sites that encourage you to send personal or financial information to these criminals.
 What is smishing?
What is smishing?
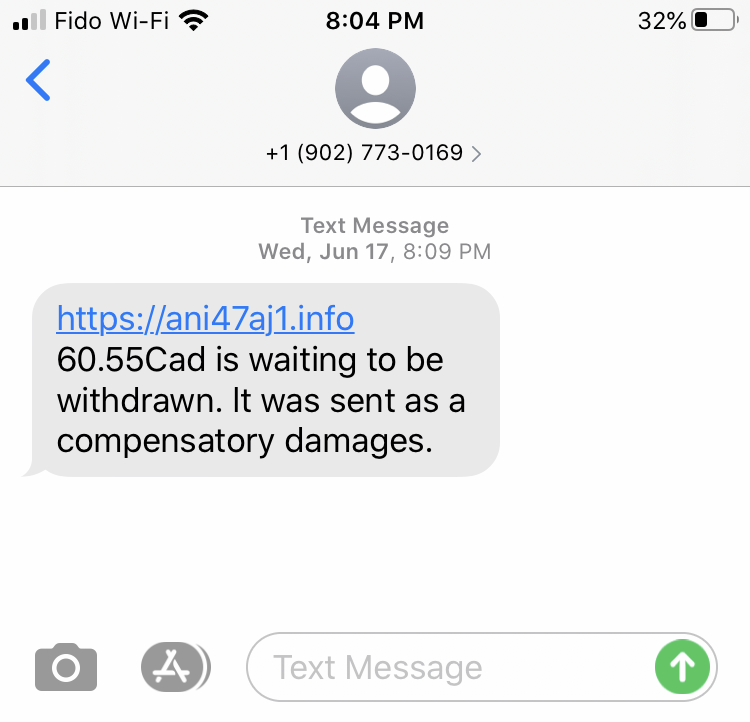
Smishing is a form of phishing that uses fake SMS (mobile phone text) messages to gain your personal information.
These messages could come from strange phone numbers you’re unfamiliar with, or masquerade as a business. These messages will often invite you to download something or click a malicious link. Cyber criminals prey on our anxieties so these smishing messages often feature a financial element indicating that you have a refund available to claim or owe money on a parking ticket.
What is vishing?
Vishing is a form of phishing that uses internet phone services (VoIP) to trick people into providing sensitive personal information such as a credit card number.
They often will create fake phone numbers to appear like a legitimate phone number. Often when not picked up, these scammers will leave an urgent message hoping it will create panic that elicits a response — namely, you phoning back. These messages can also appear positive like a message claiming you’ve won a prize. How many free cruises or flights have you appeared to have won? Other common tactics include leaving messages stating your account has been compromised and leaving a number to reset your password. Don’t fall for these common tactics.
Protect yourself from phishing attacks
- Don't trust the display name: always check the sender's actual email address. The sender's domain name (i.e. royalbank@secure.123.com) will indicate if it's a phishing attack.
- Don't click any links or attachments: hover your mouse over the link to see where the URL leads you, but don't click. Don't open any email attachments you weren't expecting.
- Check for spelling mistakes: legitimate organizations have professional communicators, so their emails typically do not contain spelling and grammar mistakes. An excess of spelling and grammar errors indicate a phishing attack.
- Be aware of urgent or threatening language: phishing attacks prey on our emotions. Invoking a sense of urgency is a common phishing tactic, so be on the lookout for subject lines like "your account has been suspended," "unauthorized login attempt," or "claim your $618.52 tax refund now."
- Review the signature: legitimate companies always provide contact details. If a signature is missing or incomplete, it may be a phishing attack.
- Never give up personal information: banks, lending institutions, insurance companies, health care services, credit card companies and government organizations will never ask for your personal information over email. If in doubt, call the organization to verify if they sent the email.
- Always be skeptical: phishing emails may have convincing logos, language and a seemingly valid email address. But just because it looks legitimate doesn't mean it is. Don't believe everything you see. If an email looks even remotely suspicious, don't open it.
- Forward phishing attacks to IST: if you get what you believe is a phishing email, forward it to abuse@ualberta.ca with the subject link “Suspected Phishing Email.” We'll let you know if it's legitimate, and if it's not, that will help us protect the next potential victim.
- Be wary of monetary requests: some phishing emails will request or demand monetary payment, often in the form of gift cards. These emails may even seem to come from a trusted contact. But be cautious with anyone asking for money or gift cards. First, pick up the phone and connect with the apparent sender to verify.
For more information on cybersecurity, visit the University of Alberta’s Chief Information Security Officer’s (CISO) website or the Canadian Centre for Cyber Security for additional tips to stay cyber-healthy.
For resources on phishing, see the following articles for more information:
- Detect Phishing Emails
- Don't fall for it - Keep an eye out for these social engineering tactics
- Don't get phished by a job opportunity scam